Bypassing MFA: The Rise of Adversary-in-the-Middle Attacks

An Adversary-in-the-Middle (AitM) phishing attack is an advanced form of credential theft in which attackers insert themselves between a user and a legitimate authentication service to intercept credentials and session tokens. This method allows attackers to bypass Multi-Factor Authentication (MFA), even when strong authentication mechanisms are in place. AitM attacks have evolved from the traditional Man-in-the-Middle attacks but incorporate more sophisticated approaches with even more malicious intent. These attacks present a significantly higher potential for severe damage.
Man-in-the-Middle vs. Adversary-in-the-Middle Attacks
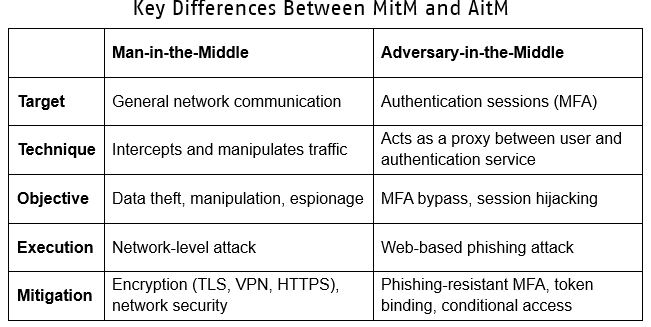
Both Man-in-the-Middle (MitM) and Adversary-in-the-Middle (AitM) attacks involve an attacker intercepting communication between two parties, but they differ in their execution, scope, and primary targets. We’ll explore some of these differences to establish a comparison of both methods and their unique objectives.
Man-in-the-Middle Attack
A MitM attack occurs when an attacker secretly intercepts and possibly alters communication between two parties without their knowledge. The attacker can passively eavesdrop or actively manipulate the data being exchanged.
The attacker intercepts the data being transferred between two communicating parties (i.e. the user and a website or the client and a server). The primary goals of an MitM attack are to steal credentials, session cookies or other sensitive information that can then be manipulated.
MitM vs. AitM: What’s the Difference?
Why MFA Doesn't Stop AitM Attacks?
MFA is a one-time barrier; therefore, once the attacker gains a session token, they no longer need to perform MFA. As the session is already hijacked, full access to the application is granted for the duration of the session. The attacker may continue to reuse the stolen session token to access the user’s account until the session expires, or the user logs out of the application.
How FIDO2 Does Prevent AitM Attacks
By implementing FIDO2/WebAuthn Authentication that leverages phishing-resistant methods to bind authentication to the device. Since no credentials, codes, or session tokens are sent over the network, it becomes impossible for an attacker to reuse stolen credentials; further, the attacker cannot generate a valid response without the legitimate device. Therefore, session hijacking, a key part of AitM attacks, becomes ineffective.
FIDO2 utilizes public-key cryptography, whereas:
- A private key is securely stored on the FIDO2 authenticator.
- A public key is registered with the website or service.
- During login, the website sends a challenge to the user’s device.
- The user’s FIDO2 authenticator signs the challenge using the private key.
Even if an attacker does successfully intercept and relay an authentication request, they cannot steal the private key because it never leaves the user’s device. Each device generates a unique private key per website. An attacker cannot export or transfer these keys to another device.
Additional Mitigation Techniques
- Implement conditional access policies to restrict logins based on device trust, geolocation, and behavioral analytics.
- Implement token binding whereby session tokens are always bound to a specific device.
- Monitor for anomalous sessions to detect and terminate suspicious logins from unknown locations or devices. Monitor for session token reuse
- Deploy network-based protections that leverage TLS inspection and zero-trust security models to detect AitM proxies.
- Implement email authentication protocols (DMARC, DKIM, SPF) to prevent spoofing.
Conclusion
MitM attacks represent a broad category of methods that specifically target network communications, while AitM phishing attacks provide a more refined approach, specifically designed to hijack authentication processes and allow attackers to bypass MFA.
Organizations should use both network security measures for MitM defense and adopt phishing resistant authentication methods that prevent MFA bypass. Enterprise security strategies that implement FIDO2 passwordless authentication will protect against these threats, as AitM techniques evolve.
Convice yourself of our expertise.
Receive the latest news and announcements about storage and security solutions as well as current events and new products.
