Authentication 101: A comparison of five well known authentication methods

In this “Authentication 101” blog post, I present selected methods for authenticating and protecting digital identities. I show where their strengths and weaknesses lie. Finally, I give a brief assessment of each method. The summary focuses mainly on the iShield Key series.
Tip: Articles worth reading on the meaning, functionality and important factors of various authentication methods can currently (as of 30.07.2024) be found at
Cloudflare What is authentication? | Cloudflare
Microsoft What Is Authentication? Definition and Methods | Microsoft Security
okta What is Authentication? Methods, Importance, & Processes | Okta
A comparison of five known authentication methods
1. Smart Card Login
Overview: Smart card login involves the use of a physical card embedded with a chip that contains encrypted authentication data. Users insert the card into a reader and often must enter a PIN to complete the authentication process.
Pros
- Security: High level of security due to encrypted data and two-factor authentication (something you have - the card, and something you know - the PIN).
- Durability: Cards are generally durable and can last several years.
- Standardization: Widely adopted in various industries, particularly in government and finance sectors.
Cons
- Cost: Initial setup and maintenance costs can be high.
- Convenience: Users must carry the card and a card reader must be available.
- Lost or Stolen Cards: If the card is lost or stolen, it can be a security risk until it is deactivated.
Use Cases
- Corporate Environments: For secure access to workstations and networks.
- Government Agencies: For accessing secure facilities and information systems.
- Financial Services: For secure transactions and data protection.
My assessment of this authentication method: Smart card login is a well-known authentication method that is widely accepted and secure. In the event of loss, it must be deactivated immediately because otherwise it represents a security risk.
2. FIDO2 Login
Overview: FIDO2 (Fast Identity Online) is an open standard for passwordless authentication. It uses public key cryptography and can involve various authenticators, such as hardware security keys (e.g. the iShield Key series - Link), biometrics, or smartphones.
Pros
- Security: High security with public key cryptography and protection against phishing and man-in-the-middle attacks.
- User Experience: Simplifies login processes by eliminating the need for passwords.
- Flexibility: Supports multiple authenticators, providing users with various options.
Cons
- Adoption: Requires support from service providers and adoption across platforms.
- Initial Cost: May involve purchasing hardware keys or upgrading infrastructure.
- Compatibility: Users need to ensure that their devices and platforms support FIDO2.
Use Cases
- Online Services: For secure login to web services and applications.
- Enterprise Environments: For passwordless access to corporate resources.
- Consumer Electronics: For secure access to personal devices and applications.
My assessment of this authentication method: The FIDO2 login has a very high level of security thanks to the public key procedure. At the same time, it simplifies the login process as a password is no longer required.
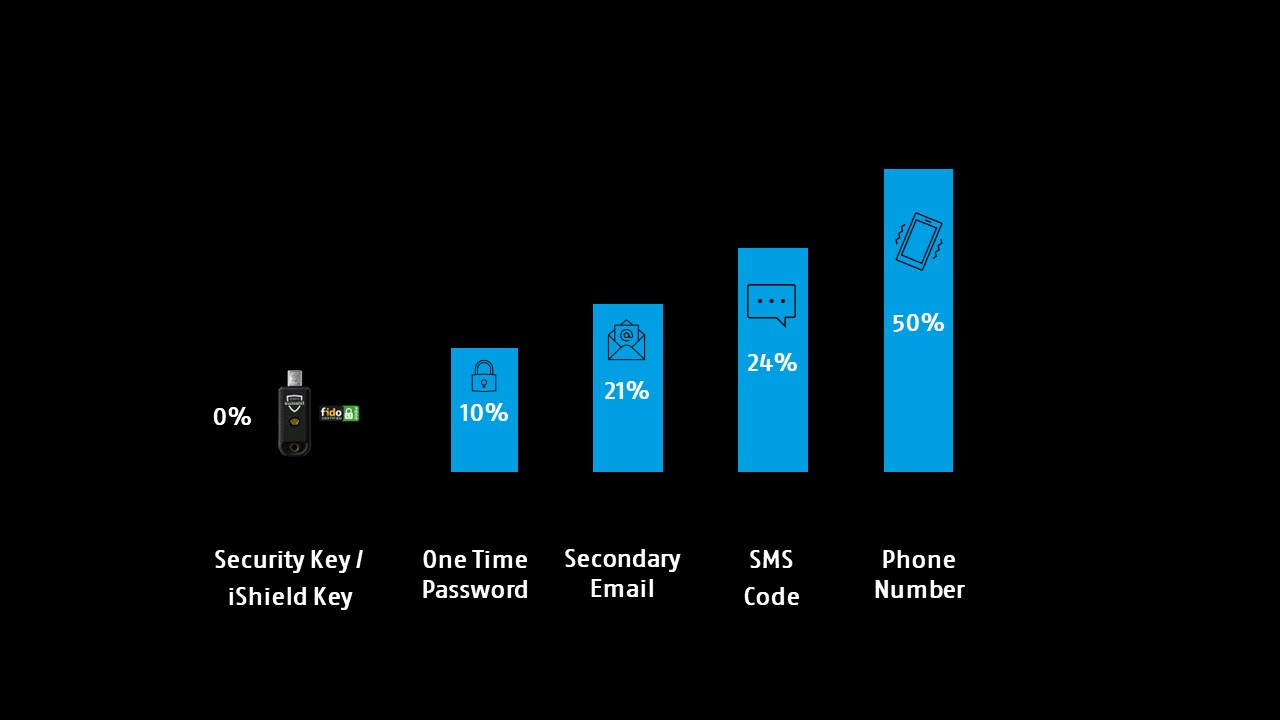
Account Takeover (ATO) risk in percentage by Multi-Factor Authentication (MFA) type
3. Out-of-Band Authentication
Overview: Out-of-band authentication involves using a separate communication channel to verify a user's identity. This often includes sending a verification code via SMS, email, or a phone call.
Pros
- Security: Adds an extra layer of security by using a separate channel from the primary authentication method.
- Ease of Use: Users are familiar with receiving codes via SMS or email.
- Cost-Effective: Generally inexpensive to implement and maintain.
Cons
- Reliability: Depends on the availability of the secondary communication channel (e.g., phone network).
- Security Risks: Vulnerable to attacks like SIM swapping, phishing, or email compromise.
- User Experience: Can be inconvenient if users do not have access to their secondary device.
Use Cases
- Banking: For verifying transactions and account access.
- Online Services: For two-factor authentication and account recovery.
- Healthcare: For secure access to patient records and systems.
My assessment of this authentication method: Out-of-band authentication is a well-known variant of two-factor authentication, which is why it requires a second communication channel (SMS, email, etc.). However, this can become a security risk due to phishing, for example.
4. Biometric Authentication
Overview: Biometric authentication uses unique biological traits such as fingerprints, facial recognition, iris scans, or voice recognition to verify identity.
Pros
- Security: High level of security due to the uniqueness of biometric traits.
- Convenience: Quick and easy for users as it doesn't require remembering passwords or carrying additional devices.
- Non-Transferable: Biometrics cannot be easily shared or stolen.
Cons
- Privacy Concerns: Potential for misuse of biometric data.
- False Positives/Negatives: Can sometimes fail to recognize the user or mistakenly identify someone else.
- Cost: Implementing biometric systems can be expensive.
Use Cases
- Smartphones: For unlocking devices and authorizing payments.
- Airports: For passenger identity verification and security checks.
- Corporate Security: For secure access to facilities and systems.
My assessment of this authentication method: Biometric authentication has a high level of security due to its biological individuality. However the implementation can be cost-intensive.
5. One-Time Password (OTP) Authentication
Overview: One-time password authentication involves generating a unique, temporary password for each login session. This can be delivered via SMS, email, or a dedicated app.
Pros
- Security: Provides an additional layer of security, especially when combined with a primary password.
- Ease of Use: Familiar to users and simple to implement.
- Flexibility: Can be used in conjunction with various authentication methods.
Cons
- Reliability: Depends on the delivery method (e.g., phone network for SMS).
- Security Risks: Vulnerable to interception or phishing attacks.
- User Experience: Can be inconvenient, especially if the OTP delivery is delayed.
Use Cases
- Online Banking: For securing transactions and account access.
- E-commerce: For verifying purchases and account changes.
- Corporate Systems: For enhancing security of VPN and remote access.
My assessment of this authentication method: One-time password authentication can be used in conjunction with other authentication methods and offers an additional layer of security, although this can be circumvented by phishing.
Conslusion
From my perspective, the FIDO2 security key is one of the strongest and most flexible hardware authentication solutions. The iShield Key by Swissbit has at least five key advantages over other authentication methods. Each authentication method has its strengths and weaknesses, and the choice of which to use often depends on the specific needs and context of the organization or user. Ultimately, a multi-factor approach that combines several authentication methods can provide the most comprehensive security of your data.
Convince yourself of our expertise.
Receive the latest news and announcements about storage and security solutions as well as current events and new products.
