Security Advisory SB-2025-02: Recording Cards
Published: 2025-10
CVSS Severity: 4.6
Summary
A vulnerability has been identified that may allow bypassing the authentication mechanism of iShield Archive and iShield Camera cards.
An adversary with local or physical access could potentially read out data from the storage, circumventing the PIN / SO-PIN login mechanism.
This vulnerability does not allow data modification or deletion.
Affected Feature
Data protection (confidentiality) feature only.
Data modification, overwriting, or erasure cannot be performed using this vulnerability.
Not Affected Features
The PIN / SO-PIN mechanism itself (authentication logic) is unaffected.
Affected Product Series
End-of-Life Products
PS-45u iShield
SFSD016GN3PM1TO-I-LF-010-SW3
SFSD032GN3PM1TO-I-HG-010-SW3
PS-66u iShield Archive
SFSD064GN1PT1MT-I-7G-07P-SW6
SFSD016GN1PT1MT-I-5E-07P-SW6
SFSD032GN1PT1MT-I-6F-07P-SW6
Products in Production
PS-66u iShield Camera
SFSD016GN1PT1TB-I-5E-06P-SW3
SFSD032GN1PT1TB-I-6F-06P-SW3
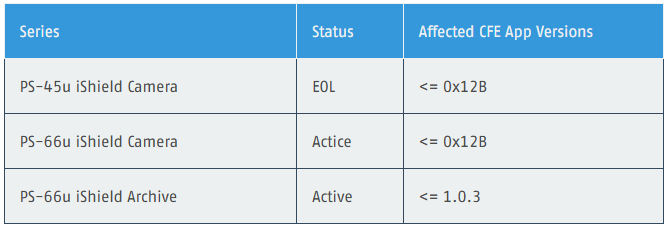
Affected Firmware Versions
Fixed Software / Mitigation
The affected firmware (CFE) cannot be upgraded in the field.
Swissbit can perform firmware patching at its facilities upon customer request.
An upgradable firmware feature is under development and will be released soon.
Products manufactured after 01.08.2025 will include the security patch and are not affected.
Using the factorty reset feature regularly via the card management tools, will erase all existing data securely, reducing the risk of data exposure
Datails on deleting and resetting the cards can be found here:
https://community.swissbit.com/c/security-functions/plug-and-play-data-encryption-ishield-archive
And here:
Exploitation and Public Disclosure
No known exploitation or public disclosure of this vulnerability has occurred.
A responsible disclosure process is ongoing with the reporting researcher.
Source and Acknowledgments
Swissbit would like to thank an independent security researcher for responsibly reporting this vulnerability.
CVSS Information
CVSS Score: 4.6 (Medium)
Vector: CVSS:3.1/AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Impact: Local attackers with physical access could gain unauthorized read-only access to data within the Private Partition.
Identification of vulnerable devices
Devices produced before August 2025 are affected. Our guide explains several ways to check the manufacturing date:
https://community.swissbit.com/c/tools-and-code/how-to-identify-the-production-date-of-your-swissbit-card
To identify vulnerable devices directly by their firmware version is described in our Firmware/Application version guide:
https://community.swissbit.com/c/tools-and-code/identification-of-firmware-application-versions-of-security-cards